2023-2024

2024: незабываемый год!
Поскольку 2024 год подходит к концу, мы в Zare хотели бы воспользоваться этим моментом, чтобы вспомнить действительно замечательный год. Это был год роста, инноваций и важных событий, которые стали возможными благодаря неизменной поддержке наших невероятных клиентов. Независимо от того, были ли вы с нами в течение десятилетия или присоединились к нам только в этом месяце. Спасибо, что вы стали неотъемлемой частью нашего пути.Этот год также ознаменовал для нас важную веху — 10 лет Zare! То, что начиналось как небольшое предприятие с собственным микроцентром обработки данных в Бристоле с емкостью всего лишь 400 серверов, превратилось в глобальную операцию, охватывающую несколько стран. С тех скромных начинаний наша мечта о работе сети мирового класса теперь стала реальностью с точками присутствия в Лондоне, Глазго, Эдинбурге, Париже, Амстердаме, Франкфурте, Цюрихе и Токио. Это был невероятный путь, и мы только начинаем!
Мы многого добились за кулисами в этом году, чтобы улучшить нашу инфраструктуру, расширить нашу сеть и предоставить новые возможности нашим клиентам. Вот некоторые из основных моментов:
Продолжение глобальной экспансии
- Развертывание в Токио: мы запустили наши первые два шкафа в Токио, предлагая решения Intel и AMD bare metal вместе с IP-транзитом. Это включало подключение к интернет-обменнику BBIX для улучшения региональной связности.
- Доступность во Франкфурте: после нескольких лет заторов серверы во Франкфурте теперь работают и доступны для развертывания!
Сетевые обновления
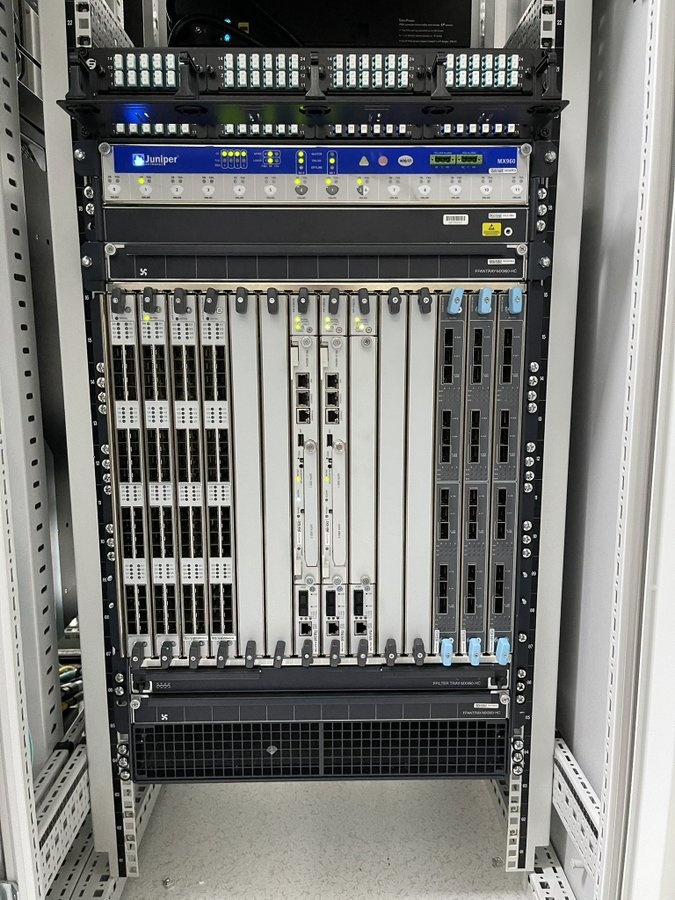
- Более высокая пропускная способность: мы модернизировали все магистральные каналы 10G до минимума 100G, что позволило сократить задержки и увеличить пропускную способность на ключевых маршрутах, включая Лондон — Эдинбург/Глазго, Эдинбург — Глазго, Франкфурт — Цюрих и Париж — Цюрих.
- Противодействие DDoS-атакам: наша общая мощность защиты от DDoS-атак резко возросла со 160 Гбит/с до ~600 Гбит/с благодаря развертыванию устройств Corero NTD1100 в нескольких местах.
- Улучшения пиринга и транзита: ключевые соединения со Swiss IX и Era IX были обновлены до интерфейсов 100G, а также добавлены дополнительные PNI с Google и Meta во вторичном местоположении, что обеспечивает лучшую избыточность и производительность. Мы также удвоили емкость с Cogent, Arelion и GTT в Лондоне до минимума 200 Гбит/с и обновили все наши соединения Cogent, Arelion и GTT во всех наших местоположениях в ЕС до интерфейсов 100G. Увеличивая нашу общую внешнюю емкость до 3,7 Тбит!
Новые серверы и разработка услуг
- Серверы с графическими процессорами: в Лондоне мы представили варианты серверов с графическими процессорами NVIDIA L4 и центральными процессорами AMD EPYC, отвечающие растущему спросу на высокопроизводительные вычисления.
- Модуль реселлеров WHMCS: по многочисленным просьбам мы запустили модуль WHMCS, который позволяет нашим клиентам-реселлерам предлагать своим клиентам лучший доступ и прозрачность своих услуг.
Эффективность и масштабируемость
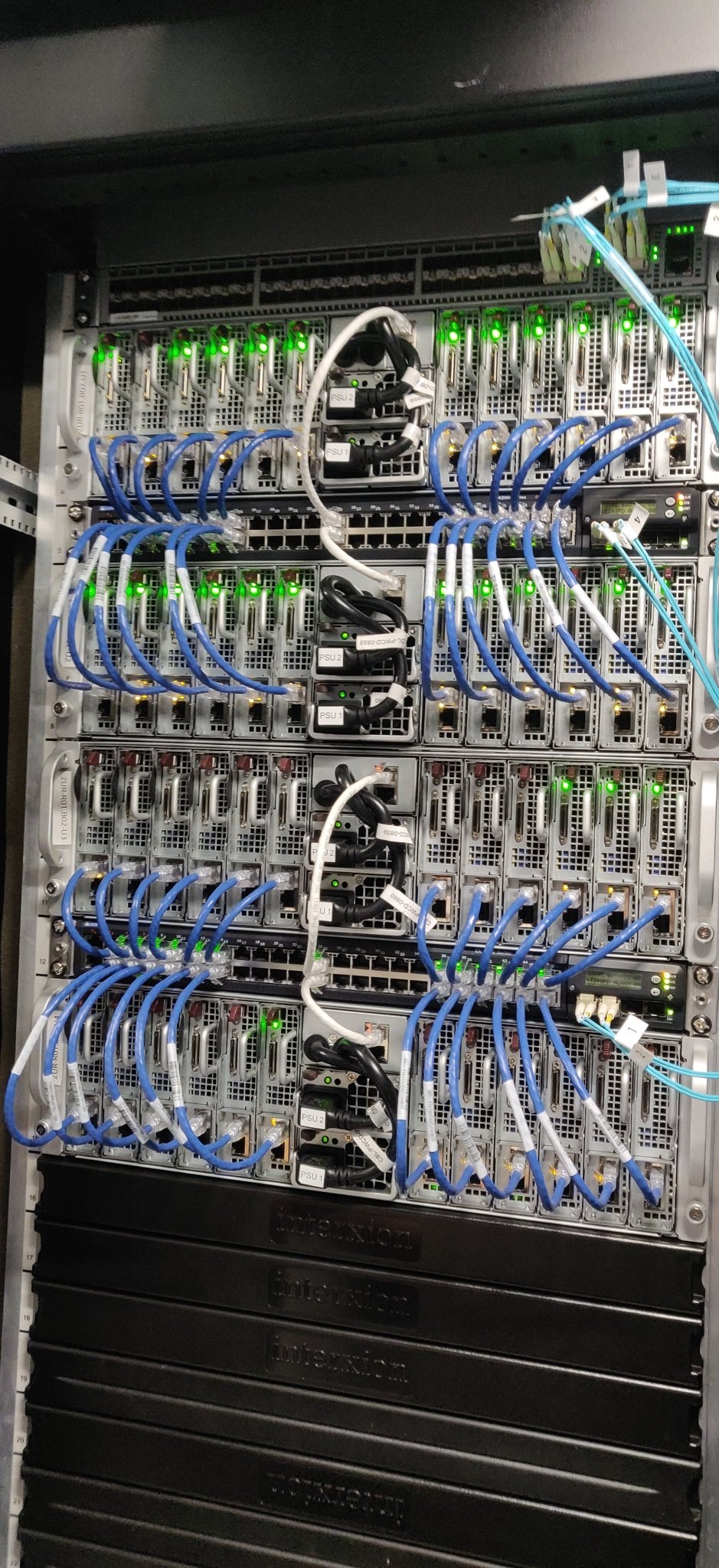
- Новые стандарты: все новые серверы Intel и AMD теперь оснащены портами 10G в стандартной комплектации, завершая эпоху 1G. Кроме того, новые шкафы оснащены 2x100G uplinks для обеспечения будущих возможностей и лучшей масштабируемости.
- Модернизация электропитания: различные шкафы в разных местах были модернизированы до трехфазных цепей питания, что повысило энергоэффективность и позволило обеспечить более высокую плотность размещения оборудования
В течение 2024 года мы также достигли нового пика пропускной способности более 500 Гбит/с в одном направлении (исключая трафик DDoS) и переслали более 2 эксабайт данных в общей сложности в течение года. Для сравнения, это эквивалентно 100 миллионам жестких дисков по 20 ГБ (что как раз соответствует емкости жесткого диска в моем первом домашнем компьютере, о, как изменились времена), поразительное достижение!
И последнее, но не менее важное: мы хотели бы поговорить о чем-то более близком к дому в нашем родном городе Бристоль. В начале этого года мы были рады присоединиться к новой инициативе, запущенной футбольным клубом Bristol City и Eleven Sports Media, чтобы привлечь местные компании в качестве партнеров сообщества. В футбольном сезоне 2024-2025 Zare является партнером сообщества футбольного клуба Bristol City! Если вы когда-нибудь окажетесь на стадионе Ashton Gate или включите одну из их телевизионных игр, обязательно обратите внимание на логотип Zare, парящий вокруг стадиона.
Оглядываясь на 2024 год, мы полны благодарности и гордости за то, чего мы достигли вместе. От небольших начинаний до пути, по которому мы идем, становясь мировым лидером в области решений bare metal, этот год стал свидетельством того, что возможно при правильном видении, решимости и поддержке.
Вперед в 2025 год!
2025: Взгляд в будущее!
Вступая в 2025 год, мы полны волнения и предвкушения возможностей, которые нас ждут. Этот год обещает стать годом роста, инноваций и постоянной приверженности предоставлению исключительных услуг нашим клиентам. Вот небольшой обзор того, что нас ждет.Расширение нашего глобального присутствия
Одной из самых ожидаемых вех 2025 года станет наше расширение в США! Вот именно, «Мерика, мы идем!» Этого ждали долго (особенно если вы помните твит, который мы сделали в 2017 году, оценивая интерес к нашему следующему местоположению!), и мы рады объявить, что Zare наконец-то представит наши решения bare metal в Северной Америке в 2025 году. Хотя точное местоположение еще не определено, Нью-Йорк является вероятным местом для нашей первой точки присутствия в США. Ожидайте ультрасовременное оборудование с новейшими процессорами AMD и Intel, поставляемое с той же надежностью и производительностью, которой вы доверяете.
Расширяем команду Zare!
Мы расширяем нашу команду! В 2025 году мы будем набирать талантливых людей на различные должности, в том числе:
- Разработчики веб-сайтов и программного обеспечения
- Техническая поддержка и системные администраторы
- Специалисты по маркетингу
Если вы увлечены технологиями или хостингом в целом и хотите стать частью пути Zare, мы будем рады услышать от вас! Свяжитесь с нами по адресу team@zare.com чтобы узнать больше.
Улучшение Zare Manager
В этом году основное внимание будет уделено созданию более интуитивного и многофункционального менеджера Zare. Планируемые улучшения включают:
- Новые инструменты и функции для оптимизации управления сервером.
- Улучшенный UI/UX для более плавного и эффективного взаимодействия с пользователем.
- Расширенные возможности реселлера, упрощающие все: от заказа новых серверов до управления существующими.
За кулисами мы разработаем и внедрим новую автоматизированную систему подготовки к работе, которая обеспечит вас новейшими и лучшими версиями ваших любимых операционных систем:
- Debian
- Ubuntu
- CentOS
- Rocky Linux
- Alma Linux
- Fedora
- Windows and more.
Расширение пропускной способности сети
Чтобы сохранить лидирующие в отрасли показатели, мы продолжим:
- При необходимости увеличьте пропускную способность сети.
- Устанавливайте новые пиринговые отношения для улучшения связи.
- Продолжать развертывание передовой инфраструктуры для удовлетворения растущего спроса.
Еще раз спасибо за то, что вы стали частью путешествия Заре. Пусть 2025 год будет фантастическим!